Viral IPhone Screen Recording Hack – Capture Sex Tapes Without Detection!
Have you ever wondered if someone could secretly record your iPhone screen without you knowing? The thought of unauthorized screen recording is terrifying, especially when it comes to intimate content. This comprehensive guide explores the alarming reality of screen capture attacks, sextortion schemes, and how to protect yourself from becoming a victim. We'll dive deep into the technical aspects, real-world examples, and most importantly, practical solutions to keep your privacy intact.
Understanding the iPhone Screen Recording Hack Threat
The Anatomy of a Screen Recording Attack
The concept of someone hacking into your iPhone to record your screen activities might sound like something from a spy movie, but it's a very real threat. When we talk about a screen recording hack, we're referring to unauthorized access to your device that allows an attacker to capture everything displayed on your screen without your knowledge or consent.
These attacks typically occur through malware that bypasses or alters the device's access controls. Once installed, the malicious software can operate silently in the background, recording your activities, capturing sensitive information, and even accessing your camera and microphone. The most disturbing aspect is that many victims don't realize they've been compromised until it's too late.
- She Lived By Never Give Up Never What Until The Leak Exposed Everything You Wont Believe What Followed
- The Nude Reality Of Iphone Xr Screen Burn In Leaked Photos Inside
Real-World Examples of Screen Recording Attacks
Consider this scenario: an attacker gains access to your device through malware that bypassed your security measures. This could happen through a malicious app, a phishing link, or even a compromised website. Once inside, the attacker can record your screen activities, capture login credentials, and access personal information stored on your device.
The consequences can be devastating. Attackers might record you during private moments, capture sensitive conversations, or document your online banking activities. They can then use this information for blackmail, identity theft, or financial fraud. The psychological impact of knowing someone has been watching your every move can be traumatic and long-lasting.
How Screen Recording Attacks Work
The Technical Process Behind Screen Capture
Screen recording attacks exploit vulnerabilities in mobile operating systems and applications. The process typically begins when malware is installed on your device, often disguised as a legitimate application or delivered through a malicious link. Once active, the malware can access the device's screen recording capabilities, camera, and microphone.
- Madison Scotts Sex Scandal Exposed Leaked Videos Lead To Public Shaming
- Exclusive Epstein Worked For Mossad The Leaked Tapes That Will Blow Your Mind
The malware operates silently, recording your screen activities in the background while you continue to use your device normally. It can capture everything from text messages and emails to video calls and browsing history. Some sophisticated malware can even record your keystrokes, providing attackers with passwords and other sensitive information.
Common Entry Points for Malware
Malware can enter your device through various channels. Third-party app stores often host applications that haven't been properly vetted for security. These apps might request excessive permissions, giving them access to your camera, microphone, and screen recording capabilities. Phishing emails and text messages can also trick users into downloading malicious software.
Public Wi-Fi networks pose another significant risk. Attackers can set up fake networks or intercept traffic on legitimate ones to deliver malware to connected devices. Once connected, they can potentially access your device and install screen recording software without your knowledge.
Personal Experience with iPhone Hacking
A Firsthand Account of Screen Recording Attack
The experience of having your iPhone hacked and screen recorded is both violating and terrifying. One victim described receiving a threatening email from someone claiming to have hacked their phone. The attacker stated they had recorded screen activities, including browsing history and personal content, and saved these recordings in the device's photo gallery.
This type of attack often begins with a threat email, where the criminal claims to have compromising information about the victim. They might say they've recorded the victim watching adult content or captured sensitive personal information. The goal is to create fear and panic, making the victim more likely to comply with demands for money or other favors.
Immediate Response to a Security Breach
When faced with a screen recording threat, immediate action is crucial. The first step should always be changing your Apple ID password and any other account passwords that might have been compromised. Enable two-factor authentication wherever possible to add an extra layer of security to your accounts.
Next, thoroughly scan your device for malware using reputable security software. Remove any suspicious applications and reset your device to factory settings if necessary. It's also wise to contact your bank and credit card companies to monitor for any unauthorized transactions that might indicate financial fraud.
Detecting Screen Recording on Your iPhone
Signs Your Device Might Be Compromised
Several warning signs can indicate that your iPhone might be under screen recording attack. Unusual battery drain is often one of the first noticeable symptoms, as malware running in the background consumes significant power. Your device might also run hotter than normal, especially when you're not using it heavily.
Another red flag is unexpected data usage. Screen recording and data transmission require substantial bandwidth, which can cause your monthly data allowance to be used up much faster than usual. You might also notice strange apps appearing on your device that you don't remember downloading.
Using Built-in Security Features
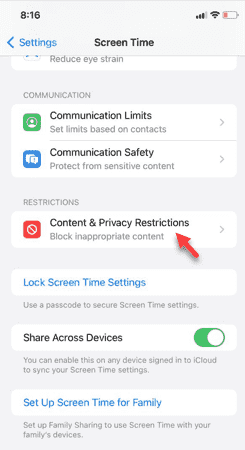
Apple provides several built-in tools to help detect and prevent unauthorized screen recording. The Screen Time feature includes communication safety settings that can detect and warn about sensitive content. When enabled, your iPhone can alert you to nude images or videos and provide warnings about potentially harmful content.
To check these settings, go to your iPhone's Settings app, tap on Screen Time, then select Communication Safety. Turning this feature on provides an additional layer of protection against inappropriate content and can help identify potential security issues.
Advanced Detection Methods
Monitoring App Permissions
Regularly reviewing app permissions is crucial for maintaining your device's security. Go through your installed applications and check what permissions each one has requested. Be particularly cautious about apps that request access to your camera, microphone, or screen recording capabilities without a clear need for those functions.
Pay attention to apps that have camera permissions but don't seem to need them for their core functionality. Mystery apps with camera permissions or those that request unusual access rights should be investigated further or removed entirely. These could be indicators of malware or spyware designed to monitor your activities.
Using Third-Party Security Software
Professional mobile security applications can provide comprehensive protection against screen recording attacks. These tools can scan your device for malware, monitor network activity, and alert you to suspicious behavior. Some advanced security apps can even detect when someone is attempting to access your camera or microphone without permission.
When choosing security software, look for reputable providers with strong track records in mobile security. Read reviews and ensure the software is regularly updated to protect against the latest threats. Remember that while security apps provide valuable protection, they should complement rather than replace good security practices.
The Sextortion Epidemic
Understanding Sextortion Schemes
Sextortion represents one of the most disturbing applications of screen recording technology. Criminals use recorded intimate content to blackmail victims, threatening to share the material with friends, family, or employers unless they receive payment. This form of extortion can begin on any platform where people communicate, from social media to dating apps.
The psychological impact of sextortion can be severe. Victims often experience anxiety, depression, and feelings of shame and helplessness. The fear of personal content being shared publicly can be overwhelming, making it difficult for victims to think clearly about their options.
How Sextortion Operations Work
Sextortion schemes typically follow a predictable pattern. The criminal establishes contact with the victim, often through social media or dating platforms. They might pose as someone interested in a romantic relationship or claim to have accidentally come across the victim's information. Once trust is established, they manipulate the victim into sharing intimate content.
With the content in hand, the criminal uses screen recording or other methods to capture the material. They then threaten to distribute it unless the victim pays a ransom, usually through cryptocurrency to maintain anonymity. The demands often escalate over time, with criminals threatening to contact the victim's contacts or post content on public platforms.
Preventing Screen Recording Attacks
Essential Security Practices
Prevention is always better than dealing with the aftermath of a security breach. Start by keeping your iPhone's operating system and all applications updated. Software updates often include security patches that address known vulnerabilities that malware could exploit for screen recording attacks.
Be cautious about the apps you download and the permissions you grant. Only install applications from the official App Store, and carefully review the permissions each app requests. If an app asks for access to features it doesn't need for its stated purpose, consider it a red flag.
Network Security Measures
Your network security plays a crucial role in preventing screen recording attacks. Avoid using public Wi-Fi networks for sensitive activities, as these networks are often targets for attackers looking to intercept data or deliver malware. If you must use public Wi-Fi, consider using a reputable VPN service to encrypt your traffic.
At home, ensure your Wi-Fi network is properly secured with a strong password and the latest encryption standards. Change your router's default administrator password and keep its firmware updated. These steps can prevent attackers from accessing your home network and potentially your connected devices.
Tools and Techniques for Screen Recording
Legitimate Screen Recording Methods
While unauthorized screen recording is a serious security concern, there are legitimate reasons to record your iPhone screen. Screen recording can be useful for creating tutorials, documenting software bugs, or saving important information. Apple provides built-in screen recording features that are secure and transparent about their operation.
To use the built-in screen recording feature, add it to your Control Center in Settings. When activated, a red indicator appears in the status bar, clearly showing that recording is in progress. This transparency ensures that everyone involved knows when screen recording is active.
Third-Party Recording Applications
Various third-party applications offer screen recording capabilities with different features and interfaces. Some provide additional functionality like scheduled recordings, audio capture, or video editing tools. However, it's crucial to choose reputable applications from trusted developers to avoid inadvertently installing malware.
When using any screen recording application, be mindful of privacy and legal considerations. Always inform others when you're recording screen activities, especially in professional or shared environments. Many jurisdictions have laws requiring consent from all parties before recording conversations or activities.
Legal and Ethical Considerations
Privacy Laws and Screen Recording
The legality of screen recording varies significantly depending on your location and the specific circumstances. Many jurisdictions require consent from all parties before recording conversations or activities. Recording someone without their knowledge or consent can result in serious legal consequences, including criminal charges and civil lawsuits.
Even in locations where one-party consent is sufficient, recording intimate activities without consent is almost universally illegal. The distribution of such recordings without consent often constitutes a criminal offense and can result in severe penalties.
Ethical Implications of Screen Recording
Beyond legal considerations, there are significant ethical implications to screen recording. Recording someone without their knowledge violates their privacy and trust. Even if you have the technical capability to record someone's screen without detection, doing so without consent is a serious breach of ethical conduct.
Consider how you would feel if someone recorded your private activities without your knowledge. The emotional and psychological impact of discovering you've been recorded without consent can be devastating. Always err on the side of transparency and obtain clear consent before recording anyone.
Advanced Protection Strategies
Implementing Multi-Layer Security
Protecting your device from screen recording attacks requires a multi-layered approach. Start with strong, unique passwords for all your accounts, and enable two-factor authentication wherever possible. This makes it much harder for attackers to gain initial access to your device or accounts.
Regular security audits of your device can help identify potential vulnerabilities before they're exploited. Check your installed applications periodically, review their permissions, and remove anything you don't recognize or no longer need. Monitor your device's behavior for signs of unusual activity.
Physical Security Measures
Physical security is often overlooked but is crucial for preventing unauthorized access to your device. Never leave your iPhone unattended in public places, and be cautious about who has physical access to your device. Use biometric authentication features like Face ID or Touch ID to prevent unauthorized access when your device is unlocked.
Consider using a privacy screen protector, which limits the viewing angle of your screen. This makes it harder for someone sitting next to you to see what's on your screen, reducing the risk of visual eavesdropping or shoulder surfing attacks.
Recovery After a Security Breach
Steps to Take If You've Been Hacked
If you discover that your iPhone has been compromised by a screen recording attack, act quickly to minimize damage. Immediately disconnect from the internet to prevent further data transmission. Change all your important passwords from a different, secure device.
Document everything you can about the breach, including when you first noticed suspicious activity and what you've observed. This information can be valuable for law enforcement investigations and for preventing future attacks. Consider filing a police report, especially if you're being extorted.
Restoring Your Device's Security
After a security breach, a thorough device reset is often necessary. Back up your important data, then perform a factory reset to remove any malware or unauthorized software. When setting up your device again, be extremely selective about what you reinstall and what permissions you grant.
Consider consulting with a professional cybersecurity expert if you're unsure about the extent of the compromise or how to properly secure your device. They can provide expert guidance on removing malware and implementing stronger security measures.
The Future of Mobile Security
Emerging Threats and Protection
As mobile devices become more powerful and integrated into our daily lives, the threats they face continue to evolve. Screen recording attacks are becoming more sophisticated, with malware that can evade detection and operate more efficiently. The rise of artificial intelligence and machine learning is creating new challenges for mobile security.
However, security technology is also advancing. New protection methods are being developed to detect and prevent screen recording attacks before they can cause harm. Apple and other manufacturers are continuously improving their security features to stay ahead of emerging threats.
Staying Ahead of Attackers
The key to staying safe from screen recording attacks is remaining vigilant and informed. Follow technology news to stay aware of the latest security threats and protection methods. Participate in security awareness training if it's available through your workplace or other organizations.
Build good security habits that become second nature. Regularly update your software, use strong passwords, be cautious about app permissions, and think critically about the links and attachments you open. These habits can significantly reduce your risk of falling victim to screen recording attacks.
Conclusion
The threat of unauthorized screen recording on iPhones is real and growing, but it's not inevitable. By understanding how these attacks work, recognizing the warning signs, and implementing strong security measures, you can significantly reduce your risk of becoming a victim. Remember that the best defense against screen recording attacks is a combination of technical protection, good security practices, and constant vigilance.
If you do experience a screen recording attack or sextortion attempt, remember that you're not alone and there are resources available to help. Law enforcement agencies are becoming increasingly sophisticated in dealing with these crimes, and there are support organizations that can provide guidance and assistance.
Your privacy and security are worth protecting. Take the time to implement the strategies discussed in this guide, and stay informed about emerging threats. With the right knowledge and tools, you can keep your iPhone and your personal information safe from unauthorized screen recording and other security threats.
- You Wont Believe This Hole To My Goal Manga Leak Censored Content Finally Revealed
- The Dark Secret Inside Epsteins Private Temple Disturbing New Leak Reveals All
Screen recording turning black : Here is Fix
![Why Is My Screen Recording Black? [Reasons and Fixes]](https://recorder.easeus.com/images_2019/article/screen-recording-tips/2023/4-3/pic.png)
Why Is My Screen Recording Black? [Reasons and Fixes]

iPhone Screen Recording NOT Working? 9 Ways to Fix It